All-in-One Installation of Kubernetes and KubeSphere on Linux
1、安装依赖
yum -y install socat conntrack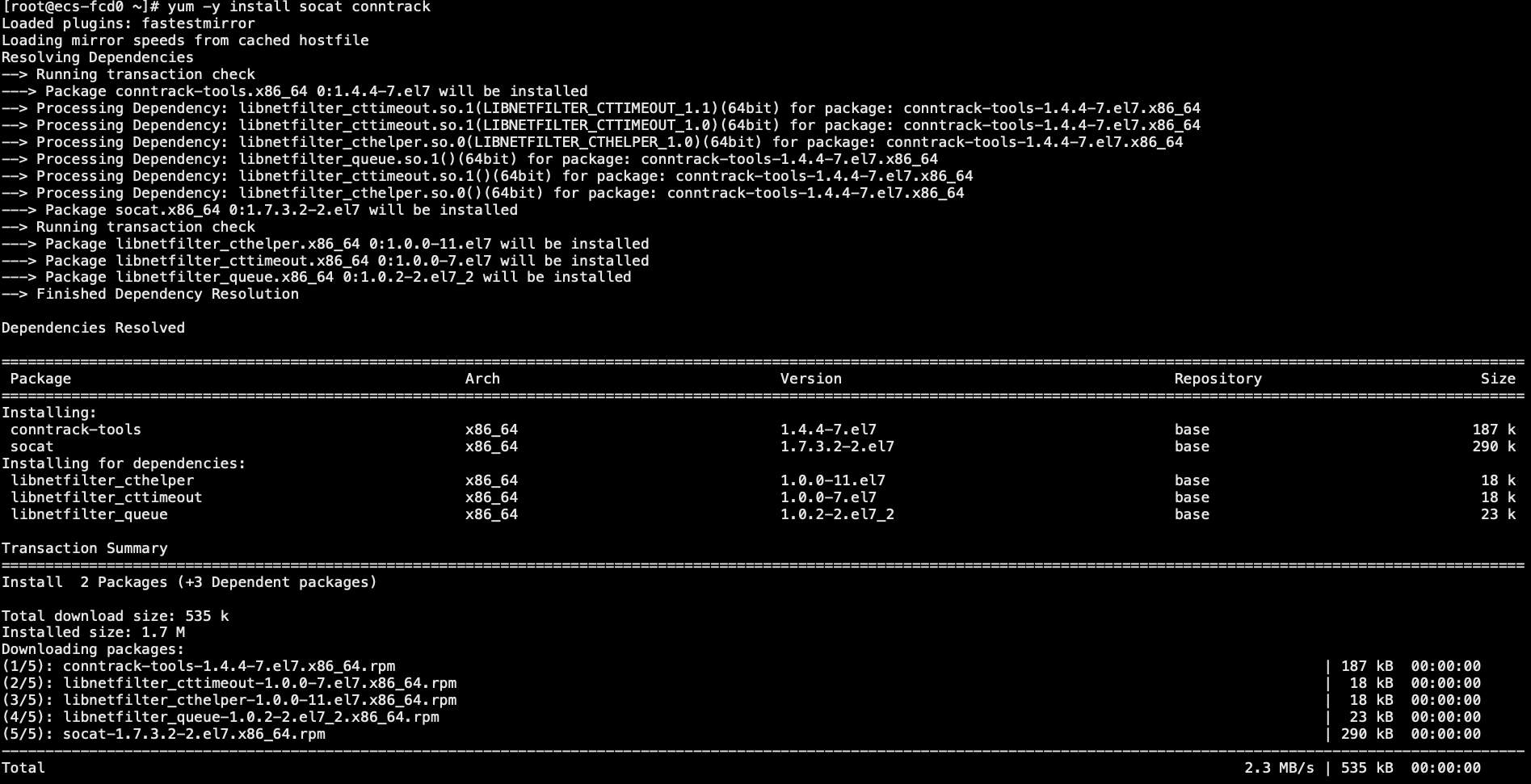
2、下载KubeKey
curl -sfL https://get-kk.kubesphere.io | VERSION=v1.1.1 sh -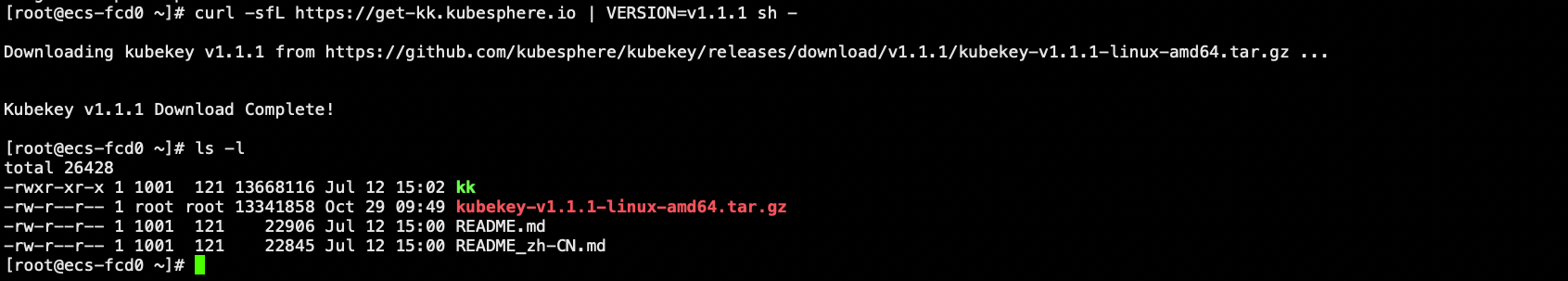
3、通过kk 命令创建集群
#### ./kk create cluster [--with-kubernetes version] [--with-kubesphere version]
./kk create cluster --with-kubernetes v1.20.4 --with-kubesphere v3.1.1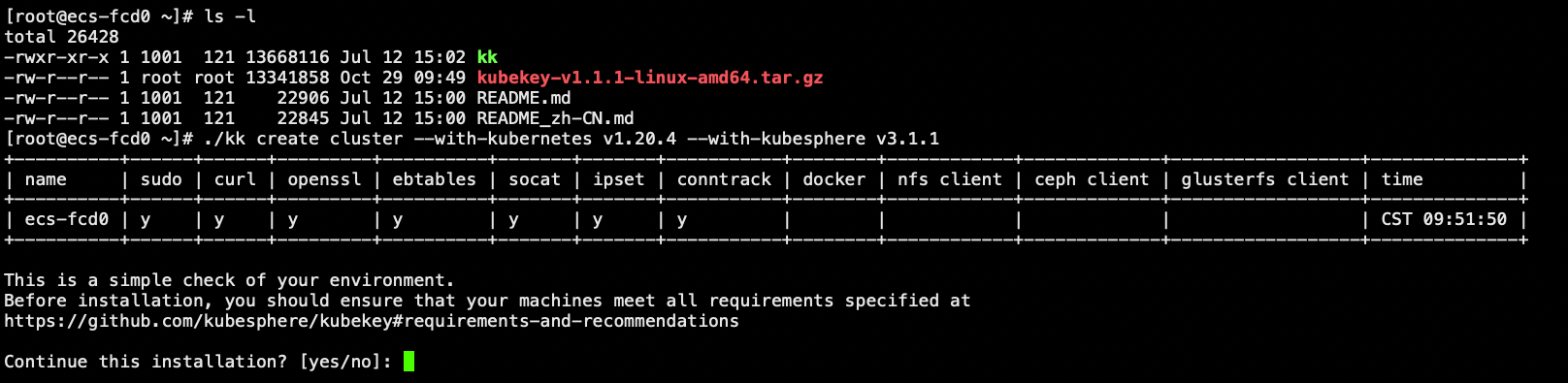
完整的输出如下:
[root@ecs-fcd0 ~]# ./kk create cluster --with-kubernetes v1.20.4 --with-kubesphere v3.1.1
+----------+------+------+---------+----------+-------+-------+-----------+--------+------------+-------------+------------------+--------------+
| name | sudo | curl | openssl | ebtables | socat | ipset | conntrack | docker | nfs client | ceph client | glusterfs client | time |
+----------+------+------+---------+----------+-------+-------+-----------+--------+------------+-------------+------------------+--------------+
| ecs-fcd0 | y | y | y | y | y | y | y | | | | | CST 09:51:50 |
+----------+------+------+---------+----------+-------+-------+-----------+--------+------------+-------------+------------------+--------------+
This is a simple check of your environment.
Before installation, you should ensure that your machines meet all requirements specified at
https://github.com/kubesphere/kubekey#requirements-and-recommendations
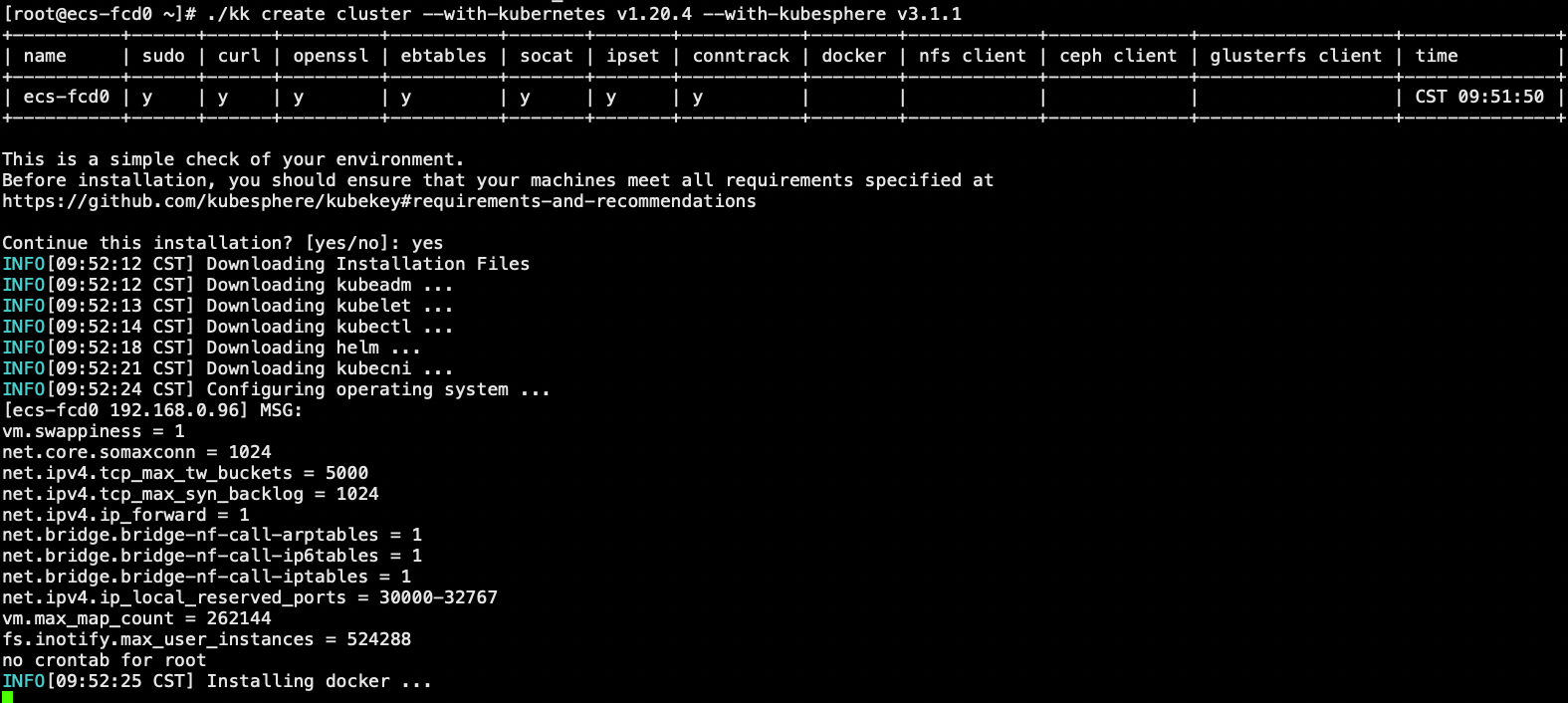
Continue this installation? [yes/no]: yes
INFO[09:52:12 CST] Downloading Installation Files
INFO[09:52:12 CST] Downloading kubeadm ...
INFO[09:52:13 CST] Downloading kubelet ...
INFO[09:52:14 CST] Downloading kubectl ...
INFO[09:52:18 CST] Downloading helm ...
INFO[09:52:21 CST] Downloading kubecni ...
INFO[09:52:24 CST] Configuring operating system ...
[ecs-fcd0 192.168.0.96] MSG:
vm.swappiness = 1
net.core.somaxconn = 1024
net.ipv4.tcp_max_tw_buckets = 5000
net.ipv4.tcp_max_syn_backlog = 1024
net.ipv4.ip_forward = 1
net.bridge.bridge-nf-call-arptables = 1
net.bridge.bridge-nf-call-ip6tables = 1
net.bridge.bridge-nf-call-iptables = 1
net.ipv4.ip_local_reserved_ports = 30000-32767
vm.max_map_count = 262144
fs.inotify.max_user_instances = 524288
no crontab for root
INFO[09:52:25 CST] Installing docker ...
INFO[09:53:06 CST] Start to download images on all nodes
[ecs-fcd0] Downloading image: kubesphere/etcd:v3.4.13
[ecs-fcd0] Downloading image: kubesphere/pause:3.2
[ecs-fcd0] Downloading image: kubesphere/kube-apiserver:v1.20.4
[ecs-fcd0] Downloading image: kubesphere/kube-controller-manager:v1.20.4
[ecs-fcd0] Downloading image: kubesphere/kube-scheduler:v1.20.4
[ecs-fcd0] Downloading image: kubesphere/kube-proxy:v1.20.4
[ecs-fcd0] Downloading image: coredns/coredns:1.6.9
[ecs-fcd0] Downloading image: kubesphere/k8s-dns-node-cache:1.15.12
[ecs-fcd0] Downloading image: calico/kube-controllers:v3.16.3
[ecs-fcd0] Downloading image: calico/cni:v3.16.3
[ecs-fcd0] Downloading image: calico/node:v3.16.3
[ecs-fcd0] Downloading image: calico/pod2daemon-flexvol:v3.16.3
INFO[09:54:39 CST] Generating etcd certs
INFO[09:54:40 CST] Synchronizing etcd certs
INFO[09:54:40 CST] Creating etcd service
[ecs-fcd0 192.168.0.96] MSG:
etcd will be installed
INFO[09:54:42 CST] Starting etcd cluster
[ecs-fcd0 192.168.0.96] MSG:
Configuration file will be created
INFO[09:54:42 CST] Refreshing etcd configuration
[ecs-fcd0 192.168.0.96] MSG:
Created symlink from /etc/systemd/system/multi-user.target.wants/etcd.service to /etc/systemd/system/etcd.service.
Waiting for etcd to start
INFO[09:54:48 CST] Backup etcd data regularly
INFO[09:54:54 CST] Get cluster status
[ecs-fcd0 192.168.0.96] MSG:
Cluster will be created.
INFO[09:54:54 CST] Installing kube binaries
Push /root/kubekey/v1.20.4/amd64/kubeadm to 192.168.0.96:/tmp/kubekey/kubeadm Done
Push /root/kubekey/v1.20.4/amd64/kubelet to 192.168.0.96:/tmp/kubekey/kubelet Done
Push /root/kubekey/v1.20.4/amd64/kubectl to 192.168.0.96:/tmp/kubekey/kubectl Done
Push /root/kubekey/v1.20.4/amd64/helm to 192.168.0.96:/tmp/kubekey/helm Done
Push /root/kubekey/v1.20.4/amd64/cni-plugins-linux-amd64-v0.8.6.tgz to 192.168.0.96:/tmp/kubekey/cni-plugins-linux-amd64-v0.8.6.tgz Done
INFO[09:54:55 CST] Initializing kubernetes cluster
[ecs-fcd0 192.168.0.96] MSG:
W1029 09:54:55.983670 10866 utils.go:69] The recommended value for "clusterDNS" in "KubeletConfiguration" is: [10.233.0.10]; the provided value is: [169.254.25.10]
[init] Using Kubernetes version: v1.20.4
[preflight] Running pre-flight checks
[WARNING SystemVerification]: this Docker version is not on the list of validated versions: 20.10.10. Latest validated version: 19.03
[preflight] Pulling images required for setting up a Kubernetes cluster
[preflight] This might take a minute or two, depending on the speed of your internet connection
[preflight] You can also perform this action in beforehand using 'kubeadm config images pull'
[certs] Using certificateDir folder "/etc/kubernetes/pki"
[certs] Generating "ca" certificate and key
[certs] Generating "apiserver" certificate and key
[certs] apiserver serving cert is signed for DNS names [ecs-fcd0 ecs-fcd0.cluster.local kubernetes kubernetes.default kubernetes.default.svc kubernetes.default.svc.cluster.local lb.kubesphere.local localhost] and IPs [10.233.0.1 192.168.0.96 127.0.0.1]
[certs] Generating "apiserver-kubelet-client" certificate and key
[certs] Generating "front-proxy-ca" certificate and key
[certs] Generating "front-proxy-client" certificate and key
[certs] External etcd mode: Skipping etcd/ca certificate authority generation
[certs] External etcd mode: Skipping etcd/server certificate generation
[certs] External etcd mode: Skipping etcd/peer certificate generation
[certs] External etcd mode: Skipping etcd/healthcheck-client certificate generation
[certs] External etcd mode: Skipping apiserver-etcd-client certificate generation
[certs] Generating "sa" key and public key
[kubeconfig] Using kubeconfig folder "/etc/kubernetes"
[kubeconfig] Writing "admin.conf" kubeconfig file
[kubeconfig] Writing "kubelet.conf" kubeconfig file
[kubeconfig] Writing "controller-manager.conf" kubeconfig file
[kubeconfig] Writing "scheduler.conf" kubeconfig file
[kubelet-start] Writing kubelet environment file with flags to file "/var/lib/kubelet/kubeadm-flags.env"
[kubelet-start] Writing kubelet configuration to file "/var/lib/kubelet/config.yaml"
[kubelet-start] Starting the kubelet
[control-plane] Using manifest folder "/etc/kubernetes/manifests"
[control-plane] Creating static Pod manifest for "kube-apiserver"
[control-plane] Creating static Pod manifest for "kube-controller-manager"
[control-plane] Creating static Pod manifest for "kube-scheduler"
[wait-control-plane] Waiting for the kubelet to boot up the control plane as static Pods from directory "/etc/kubernetes/manifests". This can take up to 4m0s
[kubelet-check] Initial timeout of 40s passed.
[apiclient] All control plane components are healthy after 53.001822 seconds
[upload-config] Storing the configuration used in ConfigMap "kubeadm-config" in the "kube-system" Namespace
[kubelet] Creating a ConfigMap "kubelet-config-1.20" in namespace kube-system with the configuration for the kubelets in the cluster
[upload-certs] Skipping phase. Please see --upload-certs
[mark-control-plane] Marking the node ecs-fcd0 as control-plane by adding the labels "node-role.kubernetes.io/master=''" and "node-role.kubernetes.io/control-plane='' (deprecated)"
[mark-control-plane] Marking the node ecs-fcd0 as control-plane by adding the taints [node-role.kubernetes.io/master:NoSchedule]
[bootstrap-token] Using token: 62vu6o.g19wdr30dbqhplwg
[bootstrap-token] Configuring bootstrap tokens, cluster-info ConfigMap, RBAC Roles
[bootstrap-token] configured RBAC rules to allow Node Bootstrap tokens to get nodes
[bootstrap-token] configured RBAC rules to allow Node Bootstrap tokens to post CSRs in order for nodes to get long term certificate credentials
[bootstrap-token] configured RBAC rules to allow the csrapprover controller automatically approve CSRs from a Node Bootstrap Token
[bootstrap-token] configured RBAC rules to allow certificate rotation for all node client certificates in the cluster
[bootstrap-token] Creating the "cluster-info" ConfigMap in the "kube-public" namespace
[kubelet-finalize] Updating "/etc/kubernetes/kubelet.conf" to point to a rotatable kubelet client certificate and key
[addons] Applied essential addon: CoreDNS
[addons] Applied essential addon: kube-proxy
Your Kubernetes control-plane has initialized successfully!
To start using your cluster, you need to run the following as a regular user:
mkdir -p $HOME/.kube
sudo cp -i /etc/kubernetes/admin.conf $HOME/.kube/config
sudo chown $(id -u):$(id -g) $HOME/.kube/config
Alternatively, if you are the root user, you can run:
export KUBECONFIG=/etc/kubernetes/admin.conf
You should now deploy a pod network to the cluster.
Run "kubectl apply -f [podnetwork].yaml" with one of the options listed at:
https://kubernetes.io/docs/concepts/cluster-administration/addons/
You can now join any number of control-plane nodes by copying certificate authorities
and service account keys on each node and then running the following as root:
kubeadm join lb.kubesphere.local:6443 --token 62vu6o.g19wdr30dbqhplwg \
--discovery-token-ca-cert-hash sha256:eee99f004db26e5d8bec17644b2b49b348d467a90b0767983408b97d18559c38 \
--control-plane
Then you can join any number of worker nodes by running the following on each as root:
kubeadm join lb.kubesphere.local:6443 --token 62vu6o.g19wdr30dbqhplwg \
--discovery-token-ca-cert-hash sha256:eee99f004db26e5d8bec17644b2b49b348d467a90b0767983408b97d18559c38
[ecs-fcd0 192.168.0.96] MSG:
node/ecs-fcd0 untainted
[ecs-fcd0 192.168.0.96] MSG:
node/ecs-fcd0 labeled
[ecs-fcd0 192.168.0.96] MSG:
service "kube-dns" deleted
[ecs-fcd0 192.168.0.96] MSG:
service/coredns created
[ecs-fcd0 192.168.0.96] MSG:
serviceaccount/nodelocaldns created
daemonset.apps/nodelocaldns created
[ecs-fcd0 192.168.0.96] MSG:
configmap/nodelocaldns created
[ecs-fcd0 192.168.0.96] MSG:
I1029 09:56:16.408843 12595 version.go:254] remote version is much newer: v1.22.3; falling back to: stable-1.20
[upload-certs] Storing the certificates in Secret "kubeadm-certs" in the "kube-system" Namespace
[upload-certs] Using certificate key:
157bef8bcef0bbc88a91fb01b50d4fdee0c6ed469cc02d22433ecafc41832e66
[ecs-fcd0 192.168.0.96] MSG:
secret/kubeadm-certs patched
[ecs-fcd0 192.168.0.96] MSG:
secret/kubeadm-certs patched
[ecs-fcd0 192.168.0.96] MSG:
secret/kubeadm-certs patched
[ecs-fcd0 192.168.0.96] MSG:
kubeadm join lb.kubesphere.local:6443 --token 1ve7n6.96wkbk60966rjqa0 --discovery-token-ca-cert-hash sha256:eee99f004db26e5d8bec17644b2b49b348d467a90b0767983408b97d18559c38
[ecs-fcd0 192.168.0.96] MSG:
ecs-fcd0 v1.20.4 [map[address:192.168.0.96 type:InternalIP] map[address:ecs-fcd0 type:Hostname]]
INFO[09:56:17 CST] Joining nodes to cluster
INFO[09:56:17 CST] Deploying network plugin ...
[ecs-fcd0 192.168.0.96] MSG:
configmap/calico-config created
customresourcedefinition.apiextensions.k8s.io/bgpconfigurations.crd.projectcalico.org created
customresourcedefinition.apiextensions.k8s.io/bgppeers.crd.projectcalico.org created
customresourcedefinition.apiextensions.k8s.io/blockaffinities.crd.projectcalico.org created
customresourcedefinition.apiextensions.k8s.io/clusterinformations.crd.projectcalico.org created
customresourcedefinition.apiextensions.k8s.io/felixconfigurations.crd.projectcalico.org created
customresourcedefinition.apiextensions.k8s.io/globalnetworkpolicies.crd.projectcalico.org created
customresourcedefinition.apiextensions.k8s.io/globalnetworksets.crd.projectcalico.org created
customresourcedefinition.apiextensions.k8s.io/hostendpoints.crd.projectcalico.org created
customresourcedefinition.apiextensions.k8s.io/ipamblocks.crd.projectcalico.org created
customresourcedefinition.apiextensions.k8s.io/ipamconfigs.crd.projectcalico.org created
customresourcedefinition.apiextensions.k8s.io/ipamhandles.crd.projectcalico.org created
customresourcedefinition.apiextensions.k8s.io/ippools.crd.projectcalico.org created
customresourcedefinition.apiextensions.k8s.io/kubecontrollersconfigurations.crd.projectcalico.org created
customresourcedefinition.apiextensions.k8s.io/networkpolicies.crd.projectcalico.org created
customresourcedefinition.apiextensions.k8s.io/networksets.crd.projectcalico.org created
clusterrole.rbac.authorization.k8s.io/calico-kube-controllers created
clusterrolebinding.rbac.authorization.k8s.io/calico-kube-controllers created
clusterrole.rbac.authorization.k8s.io/calico-node created
clusterrolebinding.rbac.authorization.k8s.io/calico-node created
daemonset.apps/calico-node created
serviceaccount/calico-node created
deployment.apps/calico-kube-controllers created
serviceaccount/calico-kube-controllers created
[ecs-fcd0 192.168.0.96] MSG:
storageclass.storage.k8s.io/local created
serviceaccount/openebs-maya-operator created
Warning: rbac.authorization.k8s.io/v1beta1 ClusterRole is deprecated in v1.17+, unavailable in v1.22+; use rbac.authorization.k8s.io/v1 ClusterRole
clusterrole.rbac.authorization.k8s.io/openebs-maya-operator created
Warning: rbac.authorization.k8s.io/v1beta1 ClusterRoleBinding is deprecated in v1.17+, unavailable in v1.22+; use rbac.authorization.k8s.io/v1 ClusterRoleBinding
clusterrolebinding.rbac.authorization.k8s.io/openebs-maya-operator created
deployment.apps/openebs-localpv-provisioner created
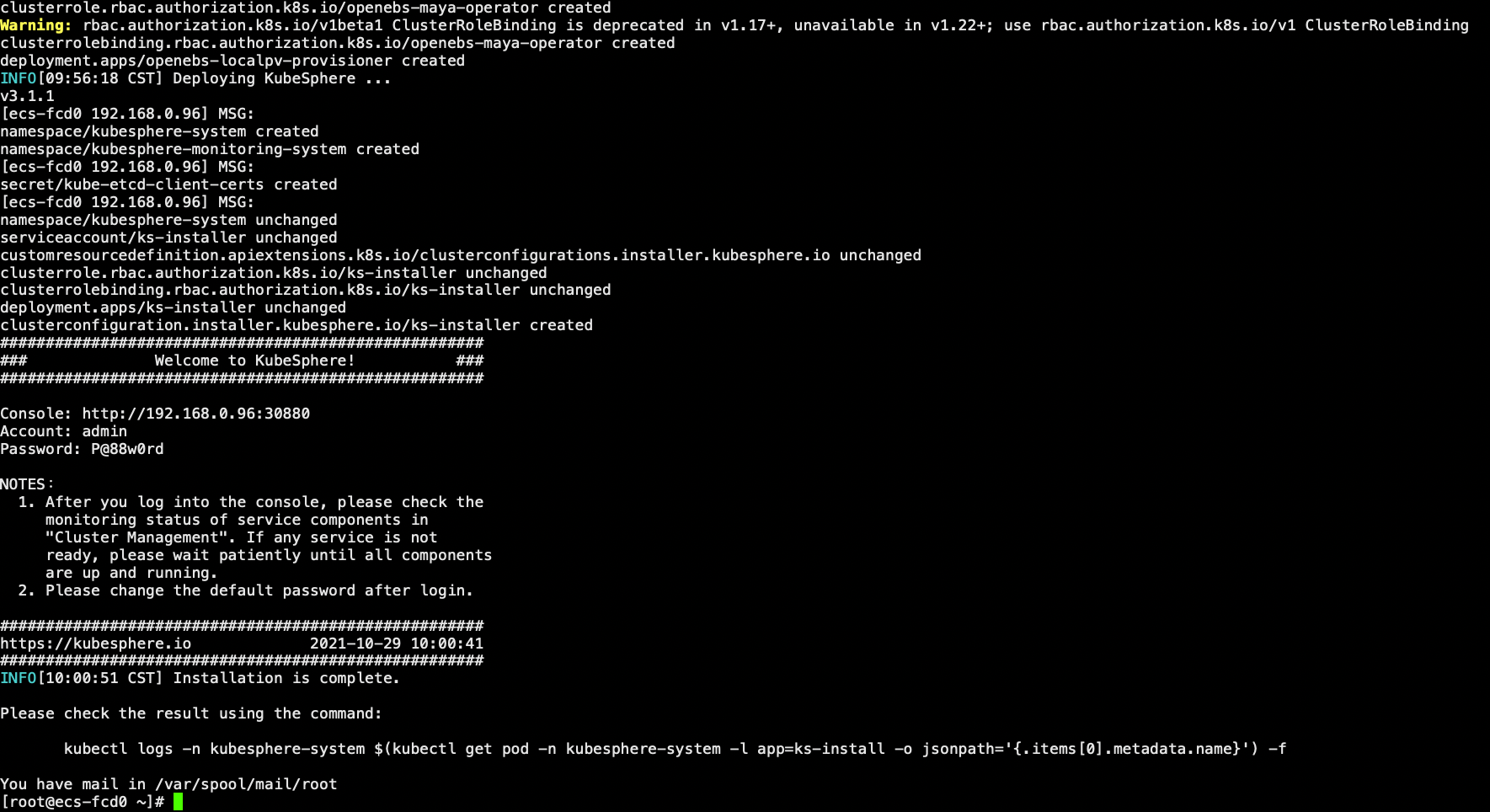
INFO[09:56:18 CST] Deploying KubeSphere ...
v3.1.1
[ecs-fcd0 192.168.0.96] MSG:
namespace/kubesphere-system created
namespace/kubesphere-monitoring-system created
[ecs-fcd0 192.168.0.96] MSG:
secret/kube-etcd-client-certs created
[ecs-fcd0 192.168.0.96] MSG:
namespace/kubesphere-system unchanged
serviceaccount/ks-installer unchanged
customresourcedefinition.apiextensions.k8s.io/clusterconfigurations.installer.kubesphere.io unchanged
clusterrole.rbac.authorization.k8s.io/ks-installer unchanged
clusterrolebinding.rbac.authorization.k8s.io/ks-installer unchanged
deployment.apps/ks-installer unchanged
clusterconfiguration.installer.kubesphere.io/ks-installer created
#####################################################
### Welcome to KubeSphere! ###
#####################################################
Console: http://192.168.0.96:30880
Account: admin
Password: P@88w0rd
NOTES:
1. After you log into the console, please check the
monitoring status of service components in
"Cluster Management". If any service is not
ready, please wait patiently until all components
are up and running.
2. Please change the default password after login.
#####################################################
https://kubesphere.io 2021-10-29 10:00:41
#####################################################
INFO[10:00:51 CST] Installation is complete.
Please check the result using the command:
kubectl logs -n kubesphere-system $(kubectl get pod -n kubesphere-system -l app=ks-install -o jsonpath='{.items[0].metadata.name}') -f检查安装结果:
kubectl logs -n kubesphere-system $(kubectl get pod -n kubesphere-system -l app=ks-install -o jsonpath='{.items[0].metadata.name}') -f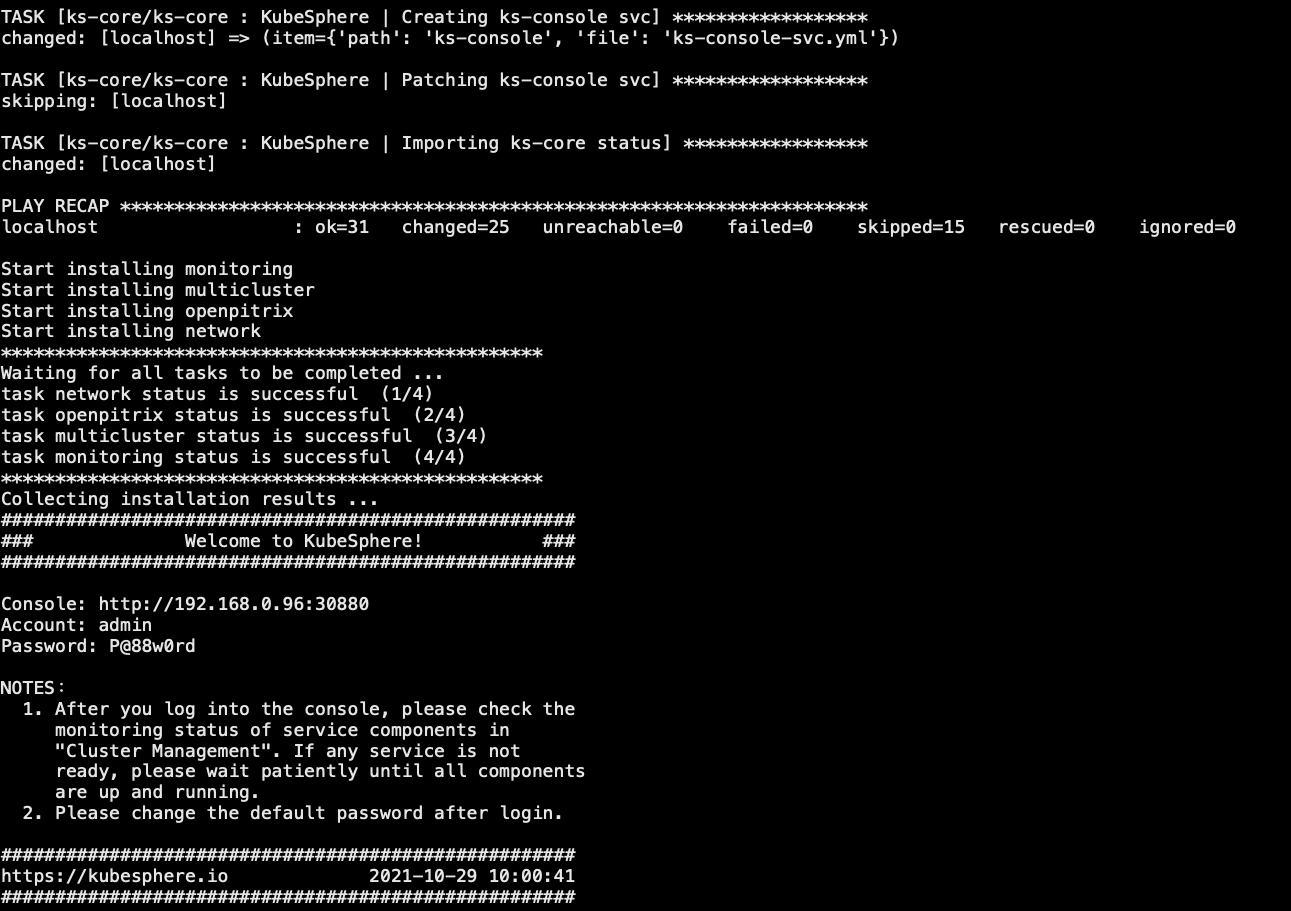
Console: http://192.168.0.96:30880
Account: admin
Password: P@88w0rd
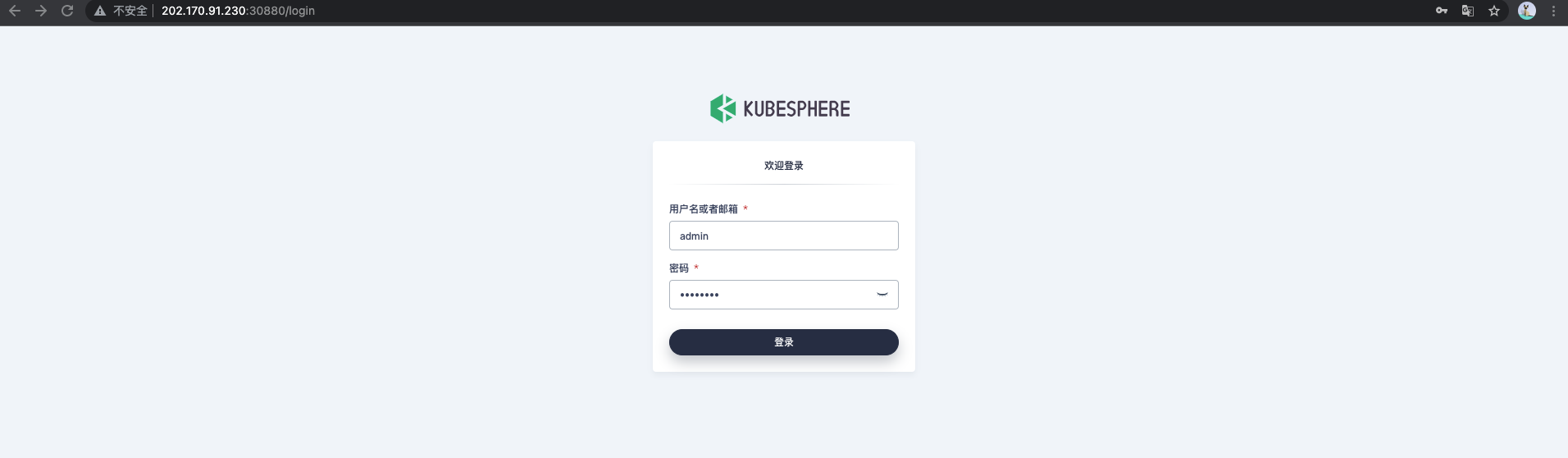
登录
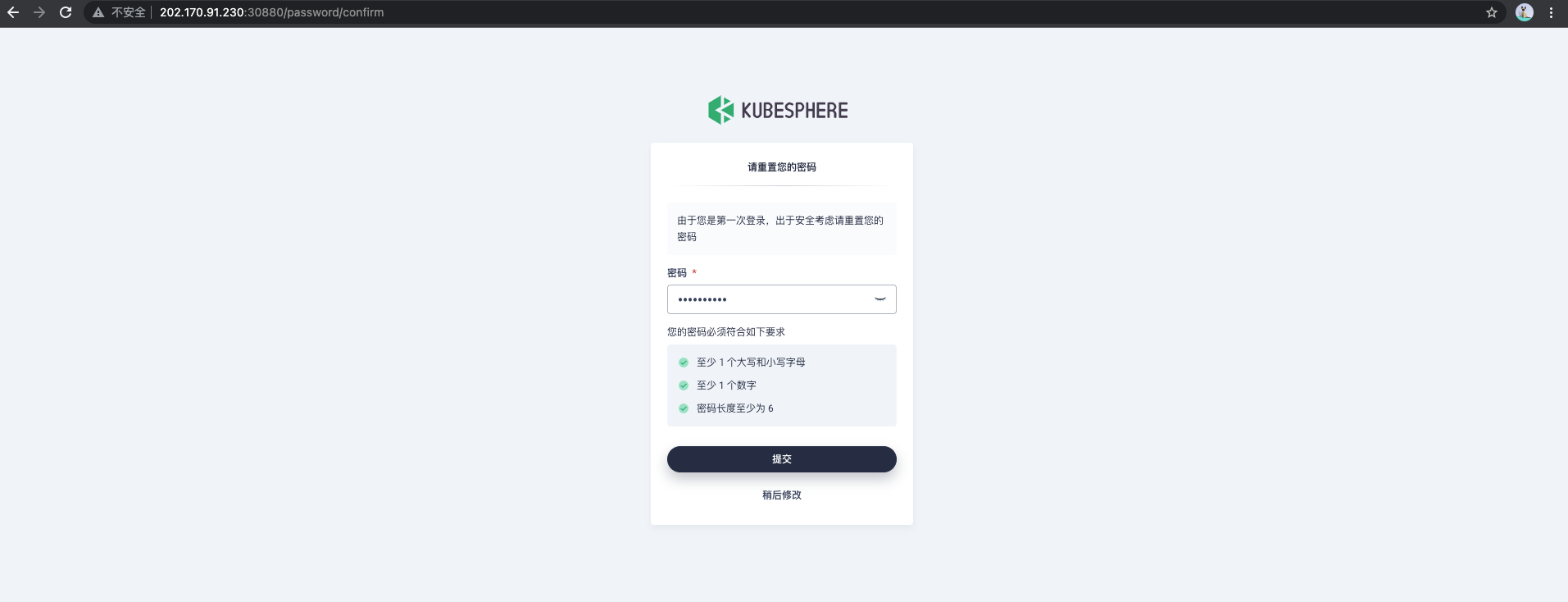
首次登陆修改密码
进入工作台
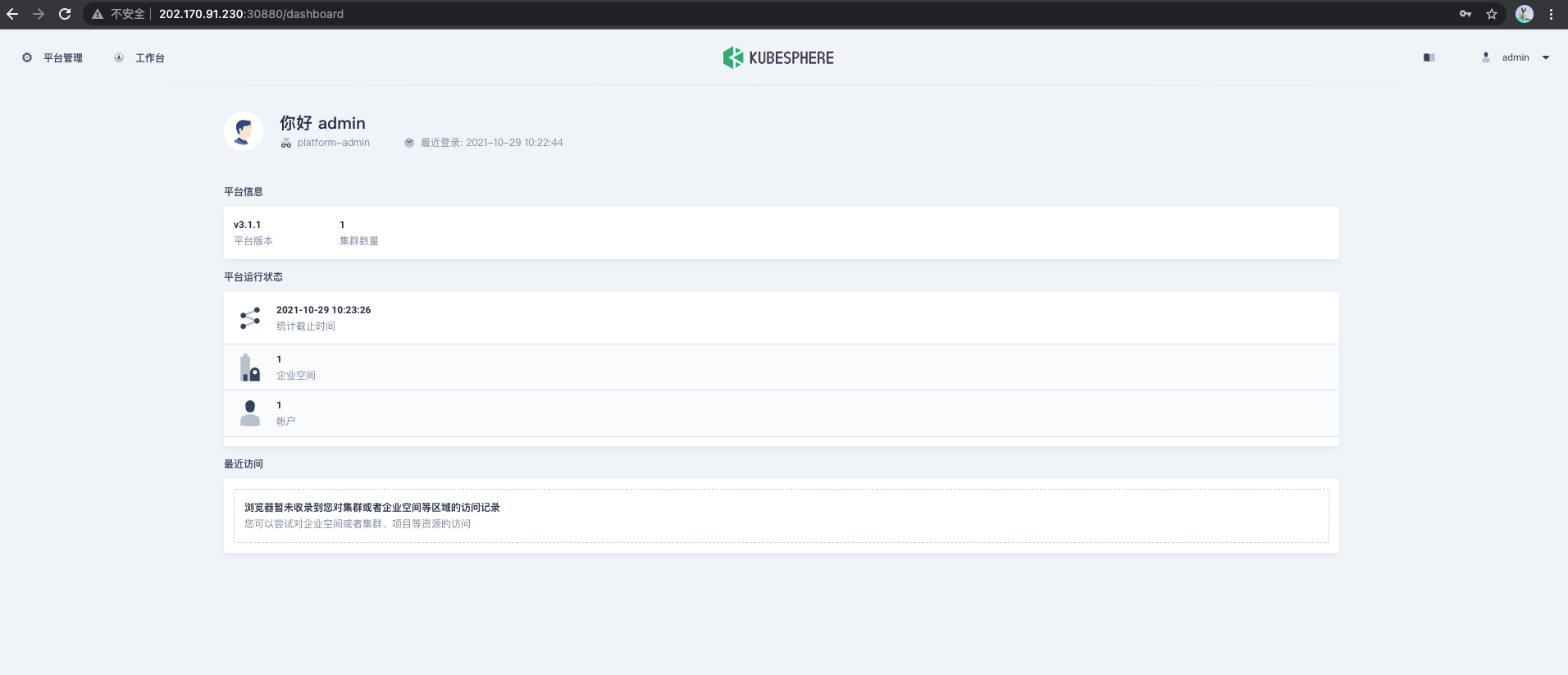
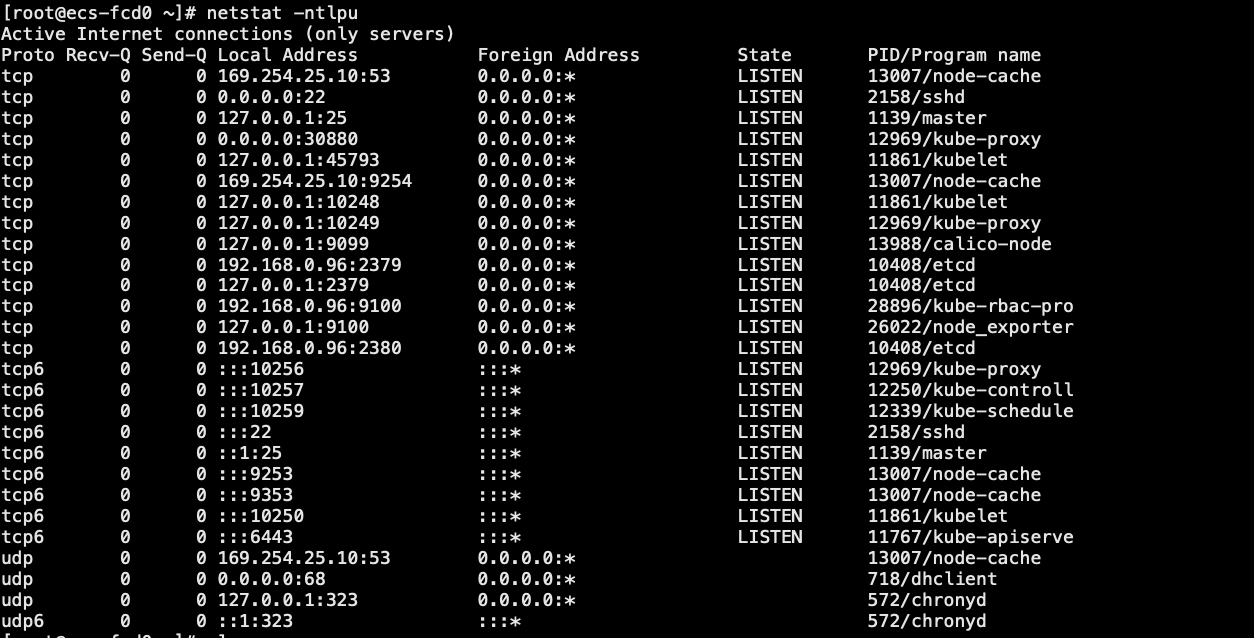
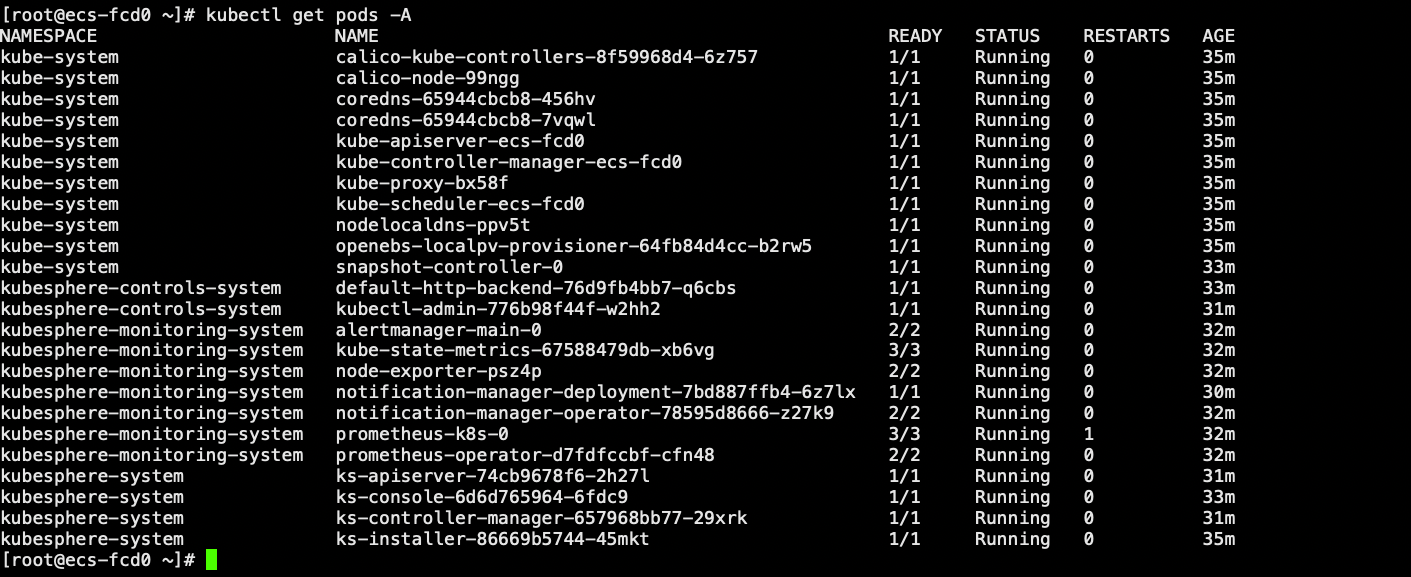
启动的服务